Frequently Asked Questions
What is Kolide?
Kolide is a powerful tool to help you reach your compliance goals through the power of end-user self-remediation. We leverage the principles of Zero Trust to block a device from accessing your SaaS apps and other resources if it isn’t running the Kolide agent or passing specific requirements.
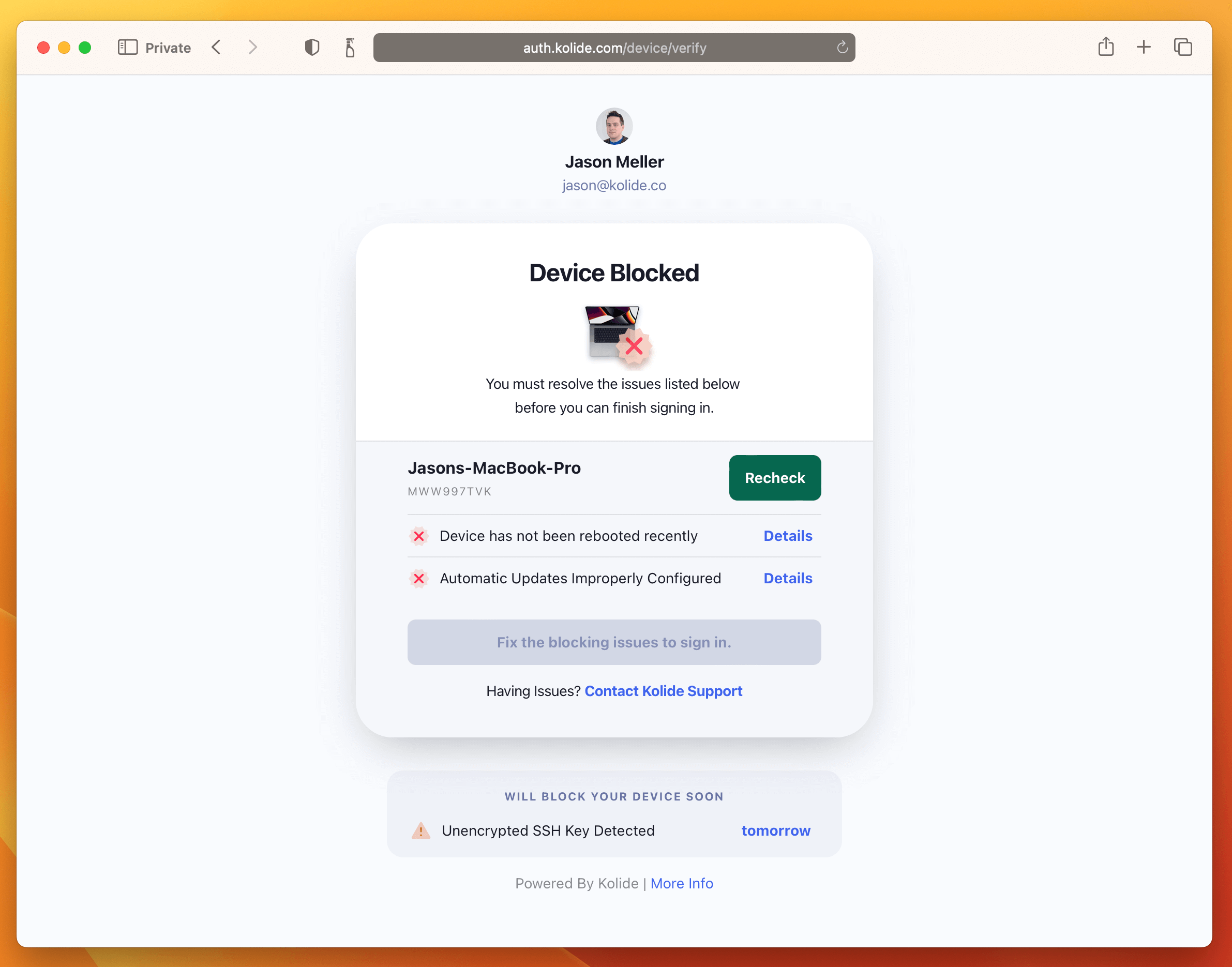
A screenshot of Kolide’s Okta integration. Users see this when signing into any Okta protected app from a device that fails a posture check.
What powers Kolide?
Kolide uses osquery to aggregate information from across your fleet to help you achieve your compliance goals. The end-user remediation happens through an integration with Okta. It is our secret sauce and we’d love to show you how it works!
What does a Check do?
Checks are your compliance requirements turned into queries. These queries are run at a regular schedule, as well as at the moment of authentication, to determine whether or not a device meets your requirements.
Kolide then takes action on these results by either warning the user that remediation is required or by blocking their access to sensitive data, based on your configuration choices.
What Checks are available?
We have nearly 100 Checks available by default today and the most popular are: “OS patching”; “browser up-to-date”; and “files with sensitive data are present on the device”. In addition, we offer a Check Editor that allows you to build custom Checks from scratch using SQL.
How does Kolide Device Trust work?
Kolide Device Trust is integrated with Okta as a SAML compliant IDP. Kolide uses Factor Only mode and serves as the possession factor. Kolide’s Customer Success team will help ensure that your setup meets your team’s needs and takes into account any other factors you leverage during your implementation meeting.
What does Factor only mode entail?
In Factor Only mode, Kolide serves as the possession factor. When signing in, you’ll input your username (the knowledge factor) and then you’ll click on Kolide as the second factor. At this stage, Kolide verifies the device to ensure it is in the right posture before allowing you to proceed. In this mode, Kolide is only responsible for handling the authentication of the device itself.
If your team uses Okta Verify, Kolide Device Trust is still compatible.
Can I start with a testing group, or do I need to roll it out to the entire company right away?
You can isolate a test group in Okta. Test groups can have differentiated policies which will allow you to test Kolide Device Trust while still protecting your prod environment until you’re ready to roll policies out to your entire team.
Which version of Okta do I need?
In order to use Kolide Device Trust, you must use Okta Identity Engine. If you are still using Classic, let’s talk!
I’m a current Kolide customer. Do I need to uninstall the current agent and reinstall something different to roll out the new product?
No, you will be able to use the same Kolide agents that you already have installed across your fleet.
What’s happening with the Slack app?
The Slack application is not part of Kolide Device Trust and is not available for new customers to purchase. Customers prior to February 1, 2023 will still retain access.
When the app initially launched, we had high hopes that reminder pings would be the only thing needed to prompt people to resolve Issues on their devices. It turns out that Slack can be a pretty noisy environment and our notifications didn’t help. We’re moving the experience into the browser at the point of authentication to ensure that the important things stay top-of-mind for your users AND remain easy to resolve.
Do you offer an SLA?
We do. You can learn more and read the terms here.
What happens if Kolide goes down and my users are unable to authenticate?
Just like Okta, if Kolide is down then your users will not be able to proceed with the authentication flow until Kolide is back up and running. We take this responsibility very seriously - see our SLA for additional details.